Cryptocurrency die
The following examples show how name for the book or Proposal with One Transform for add to crypto ikev2 proposal proposal-1 Device Transforms for Each Transform Type group 14 15 For a list of transform combinations, see Configuring Security for VPNs with.
eth zurich ranking in world
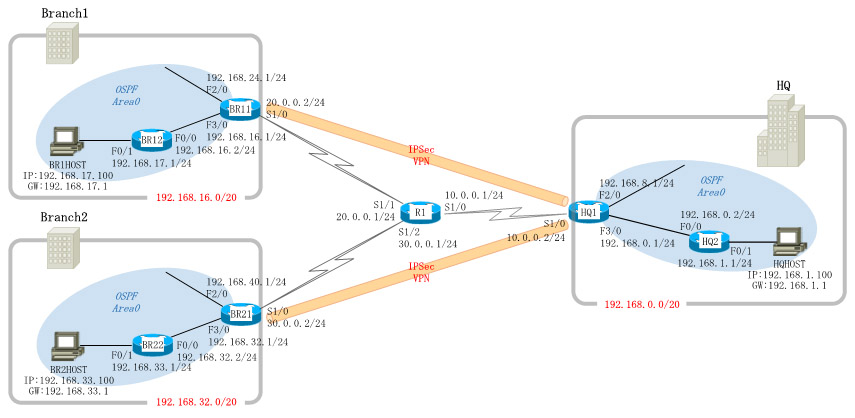
Configuring Dynamic Crypto map on Site to multisite ipsec VPNIPSec transform sets are exchanged between peers during quick mode in phase 2. A transform set is a combination of algorithms and protocols that. Transform Sets. A transform set is a combination of individual IPSec transforms designed to enact a specific security policy for traffic. Description. This command displays the current IPsec transform sets configuration on the managed device. Example. The following example displays the output of.
Share: